When discussing cybersecurity threats, most businesses focus on external attackers such as hackers, malware, and phishing scams. However, one of the most significant security risks comes from within—insider threats. Employees, whether malicious or negligent, can cause data breaches, financial losses, and reputational damage. In 2025, organizations must recognize and mitigate insider threats to protect their sensitive information and maintain operational security.
What is an Insider Threat?
An insider threat occurs when an individual within an organization—such as an employee, contractor, or business partner—misuses their access to harm the company’s data, systems, or reputation. These threats can be intentional or accidental, but both can have severe consequences.
Types of Insider Threats
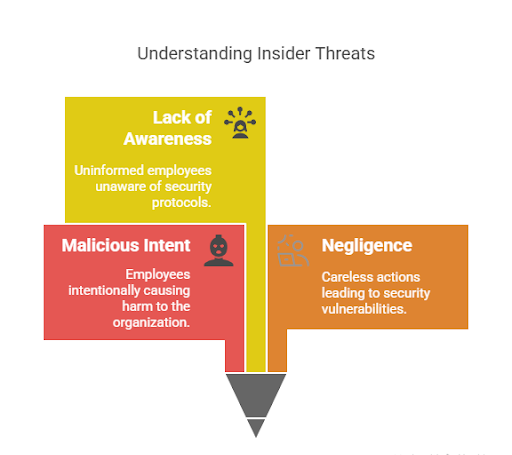
- Malicious Insiders – Employees or former staff members who intentionally leak or misuse company data for personal gain, revenge, or corporate espionage.
- Negligent Insiders – Workers who unintentionally compromise security by mishandling sensitive information, falling for phishing scams, or failing to follow security protocols.
- Compromised Insiders – Employees whose accounts have been hacked or credentials stolen, allowing cybercriminals to access internal systems without detection.
Why Insider Threats Are a Growing Concern in 2025
1. Increased Remote Work and BYOD Policies
With more employees working remotely and using personal devices, organizations face greater risks of unauthorized data access, unsecured networks, and lack of oversight.
2. Rising Cases of Data Leaks and Corporate Espionage
Many industries are seeing an increase in data leaks caused by disgruntled employees or external competitors bribing insiders to share confidential information.
3. Poor Cybersecurity Awareness Among Employees
Human error remains one of the biggest contributors to security breaches. Employees who are unaware of cybersecurity best practices may accidentally expose critical data.
4. Lack of Insider Threat Detection Systems
Many businesses focus on external threats while failing to implement monitoring tools that detect suspicious behavior from within the organization.
How to Mitigate Insider Threats
1. Implement Strict Access Controls
Limit employee access to sensitive data based on their roles. Use role-based access control (RBAC) to ensure that only authorized personnel can access critical systems.
2. Conduct Regular Employee Training
Educate employees about cybersecurity best practices, phishing threats, and data protection policies to reduce the risk of accidental breaches.
3. Monitor and Detect Suspicious Activity
Utilize User and Entity Behavior Analytics (UEBA) to track unusual login patterns, data transfers, and unauthorized access attempts.
4. Enforce Strong Authentication Measures
Use multi-factor authentication (MFA) and secure password policies to protect employee accounts from being compromised.
5. Establish a Clear Insider Threat Policy
Develop and enforce policies that outline acceptable use of company data, consequences of data mishandling, and procedures for reporting suspicious activities.
6. Invest in Advanced Cybersecurity Solutions
Using comprehensive cybersecurity platforms like Ovron Total Security can help businesses detect and mitigate insider threats before they cause significant damage.
Conclusion
Insider threats pose a significant cybersecurity risk that businesses cannot afford to ignore. Whether intentional or accidental, security breaches from within can be just as damaging as external cyberattacks. By implementing strict security policies, employee training programs, and advanced threat detection tools, organizations can safeguard their sensitive data. Partnering with trusted cybersecurity providers like Ovron Total Security ensures that businesses remain protected against insider threats and other evolving security risks.
In today’s digital world, taking proactive steps against insider threats is essential for maintaining data security, business continuity, and customer trust.
Follow us on Social Media:
For more details, connect with us:


